EdgeBit gives developers context about new and modified software dependencies when submitted a pull request or pushing a new commit before it merges into main.
This context is useful for:
- vulnerabilities: understand vulnerabilities present in the selected version(s)
- recommendations: see a recommended version with fixed vulnerabilities, if available
- standardization: gain context about versions of the same dependency that other teams may be using at your organization – think of this as a gentle nudge to standarize via social proof
This document will walk through setting up a generic pipeline runner that can run CLI binaries.
This guide will use the Syft open source project to generate the software bill of materials (SBOM) and the EdgeBit CLI to upload them.
Setting Up the Pipeline
First, in the EdgeBit Console, generate a new Access Token for this repository to use. You can find this in the left hand navigation under “Access Tokens”.
Install the CLI tools:
# Install ebctl
$ curl -sL https://install.edgebit.io/releases/edgebit-cli/v0.8.1/edgebit-cli_Linux_x86_64.tar.gz --output ebctl.tar.gz
$ tar -xvf ebctl.tar.gz
# Install syft v1.4.0
$ curl -sSfL https://raw.githubusercontent.com/anchore/syft/main/install.sh | sh -s -- -b . v1.4.0
In your code repo, create ./edgebit/container-syft.yaml with the default config file.
$ mkdir -p .edgebit
$ curl -sL https://edgebit.io/docs/0.x/assets/container-syft.yaml > ./edgebit/container-syft.yaml
Create the Software Bill of Materials
In your pipeline, run the following commands to generate an SBOM after your container or project is built:
$ export IMAGE='registry.example.com/foo:latest'
$ export NAME='foo'
$ docker build -t $IMAGE .
$ syft \
scan $IMAGE \
--config ./edgebit/container-syft.yaml \
--output spdx-json=$NAME.spdx.json
Upload to EdgeBit
Next, compile some commit info in order to identify where this SBOM was generated from:
$ BASE_BRANCH='main'
$ BASE_SHA=$(git merge-base --fork-point $BASE_BRANCH)
$ LATEST_SHA=$(git rev-parse HEAD)
Upload the SBOM using the ebctl tool:
$ export EDGEBIT_API_KEY='dnrekvq95CJ6_JcVixpfTEx8L3k3hDsggoqSr'
$ export EDGEBIT_URL='https://foo.edgebit.io'
$ ebctl upload-sbom \
--component $NAME \
--tag latest \
--repo https://github.com/org/repo \
--commit $LATEST_SHA \
--image-tag $IMAGE \
--image-id $(docker image inspect --format '{{.ID}}' $IMAGE) \
--repo-digest $(docker image inspect --format '{{join .RepoDigests ","}}' $IMAGE) \
$NAME.spdx.json
Test the EdgeBit Bot
Create a new branch and commit the changes to watch your pipeline run.
Set Up the GitHub app
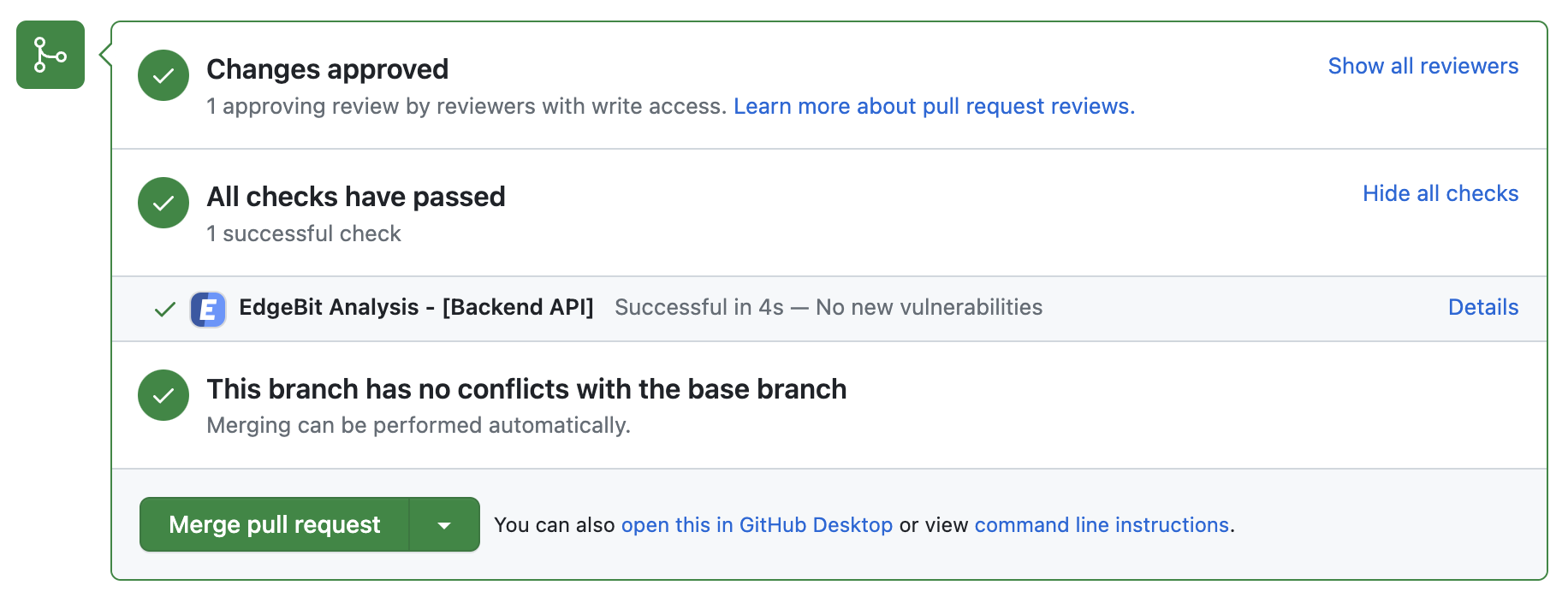
Optionally, use the EdgeBit’s GitHub app to allow Developers to see a new EdgeBit check on their PRs:
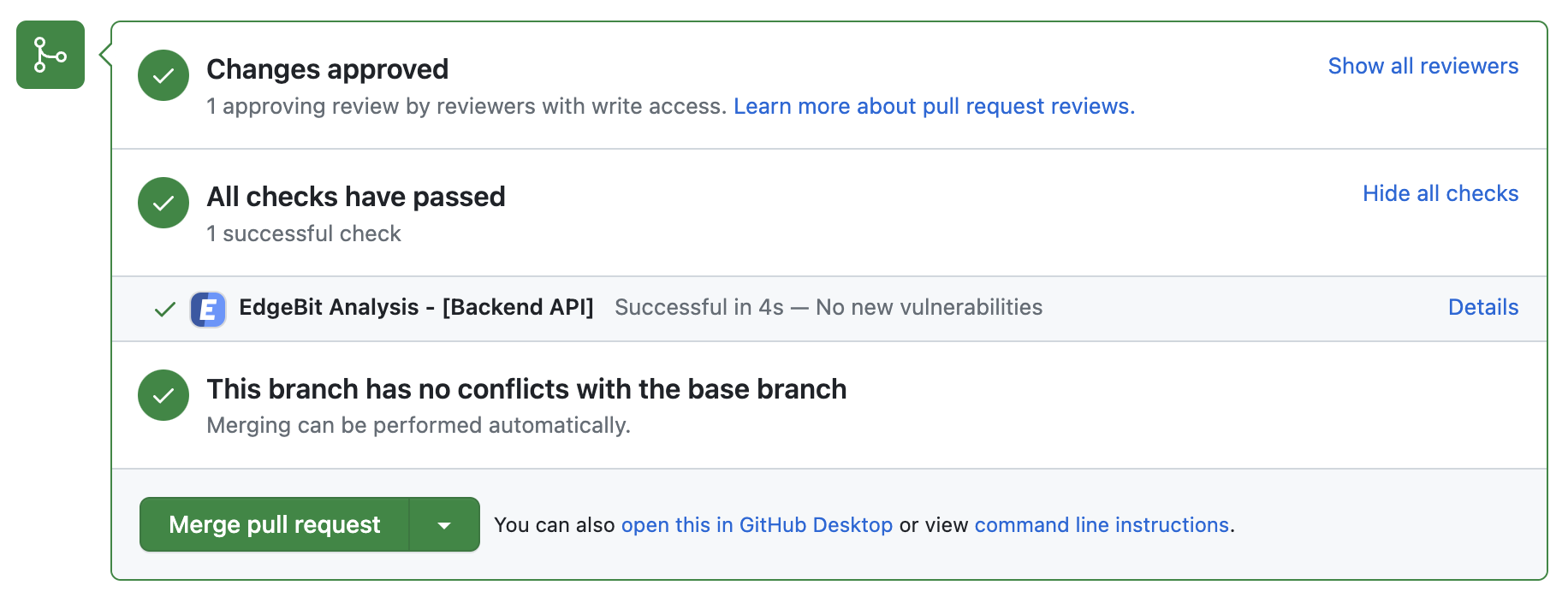
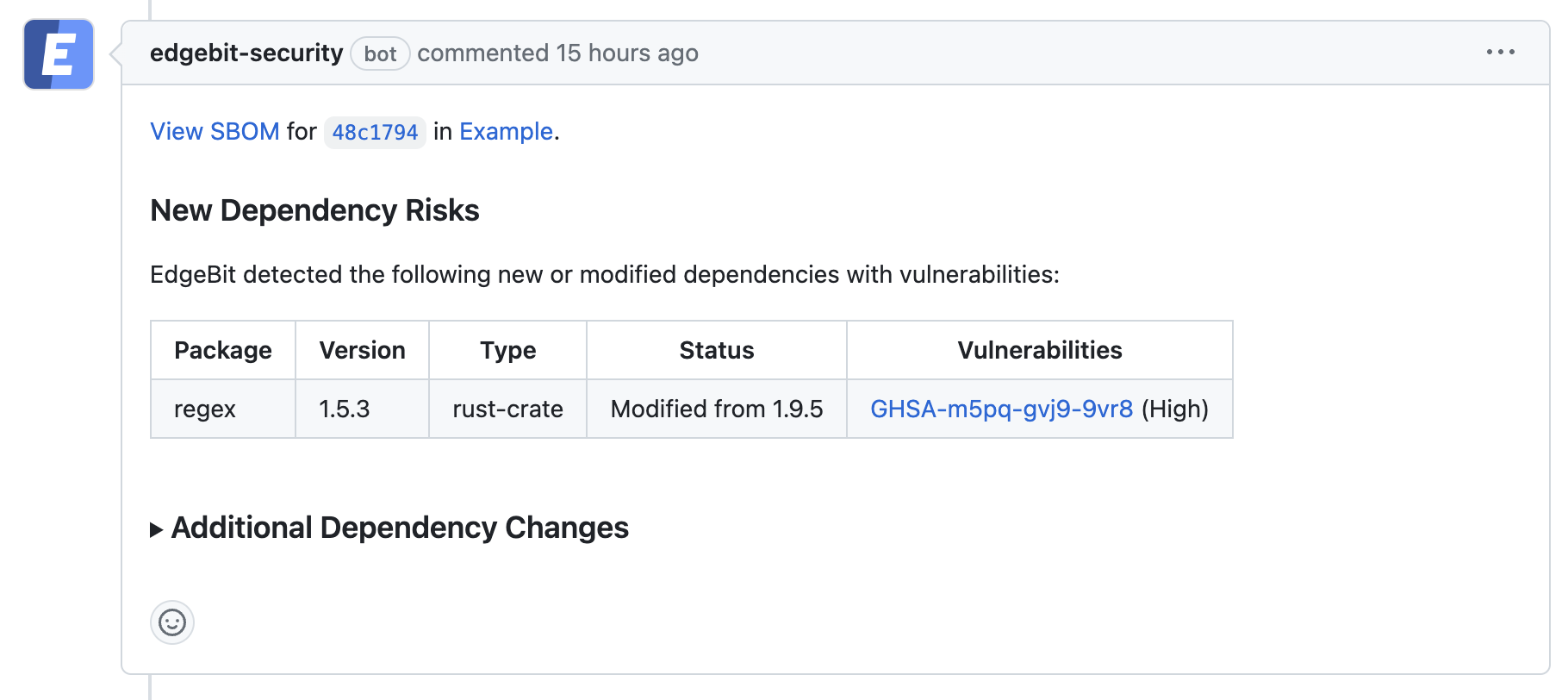
- Comments on the PR if new dependency changes are detected, highlighting:
- New vulnerabilities and supply chain risks introduced by the changes
- Confirming addition, modification or removal of dependency changes without issues
- Link to more detail within EdgeBit about the current state of all known vulnerabilities
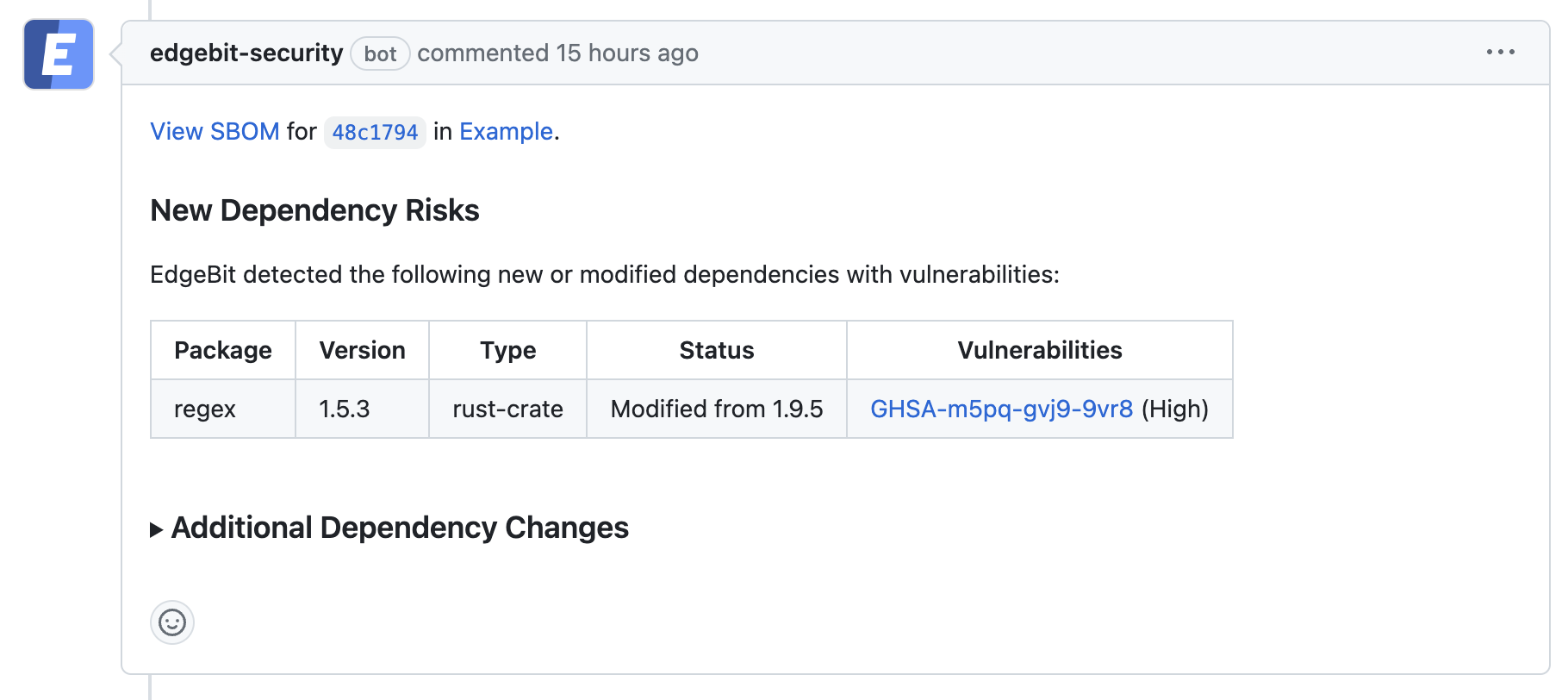
If a PR makes dependency changes and new issues are found, EdgeBit will comment with more information:
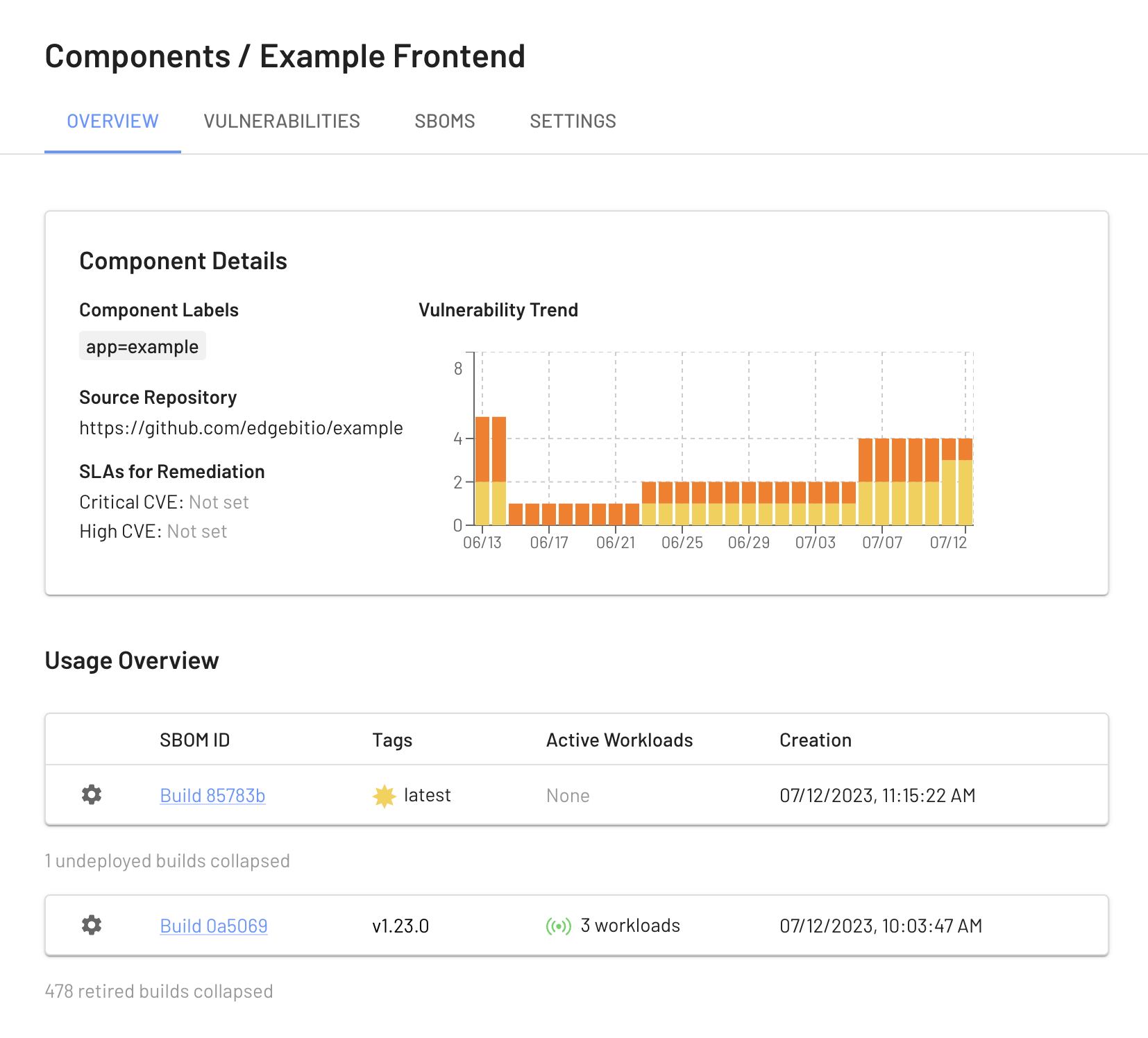
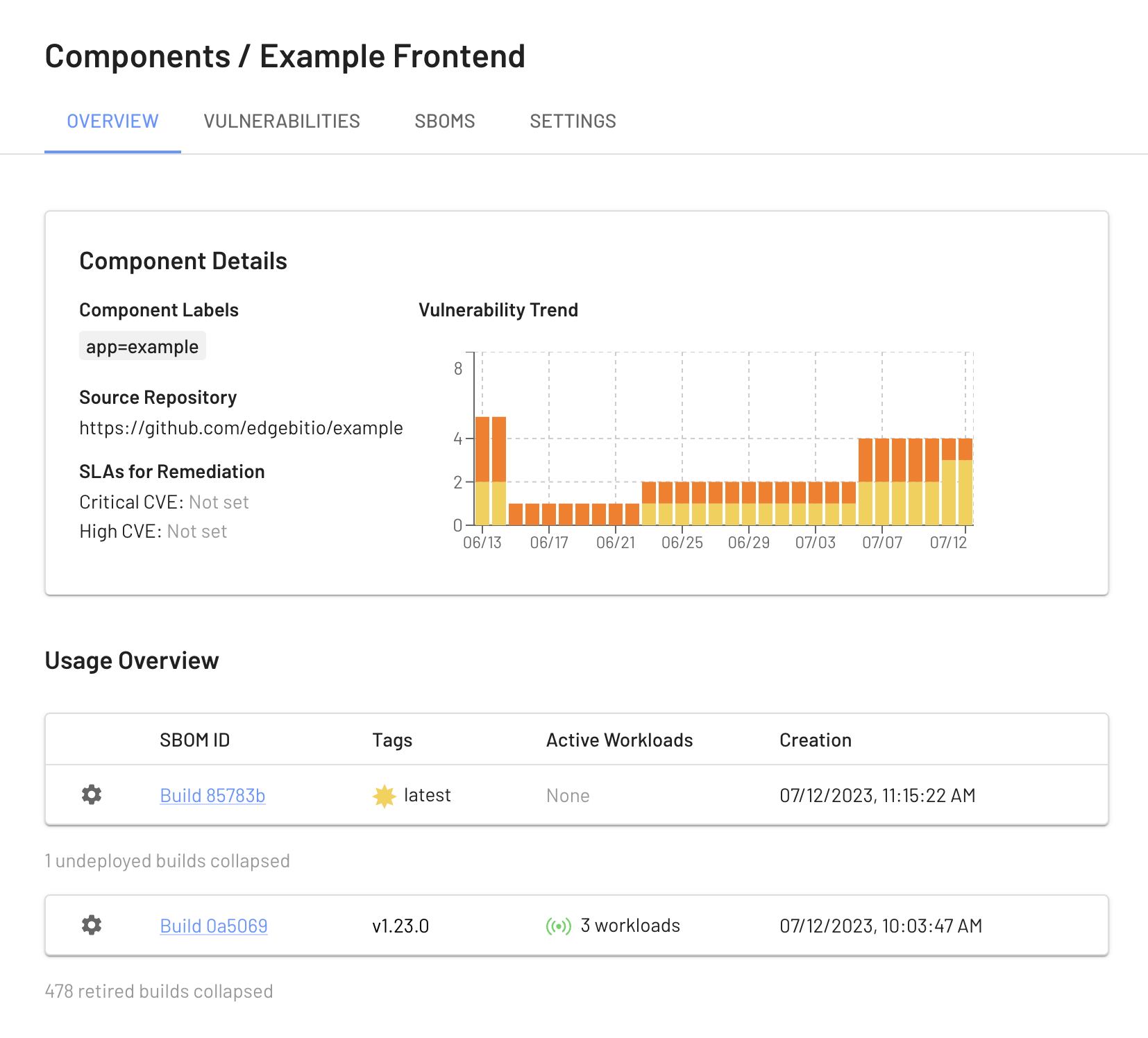
View your Build Artifacts in the EdgeBit Console
Your EdgeBit Console contains reports about each SBOM uploaded and the current state of all vulnerabilities in your software Components.
Next: Install Machine Agent